It’s never late to become safe. As technology penetrates our lives and business deeper and more profound each day, so do risks associated with adopting hi-tech innovations. The Internet of Things (IoT) encomapses a wide range of smart devices, but they are not as intelligent as we would like them to be when it comes to cybersecurity. Check out what we’ve got to say on this issue.
written by:
Anastasia Borodinets
It’s never late to become safe. As technology penetrates our lives and business deeper and more profound each day, so do risks associated with adopting hi-tech innovations. The Internet of Things (IoT) encomapses a wide range of smart devices, but they are not as intelligent as we would like them to be when it comes to cybersecurity. Check out what we’ve got to say on this issue.
In our previous articles (they are here and here if you haven’t read them yet) we covered some general issues of IoT device security and what measure should be taken to secure them, including blockchain and certification. Moreover, we compiled a general overview of actions each party involved in implementing IoT projects can take for a safer IoT world. Now let’s study it in more detail.
Everybody Counts
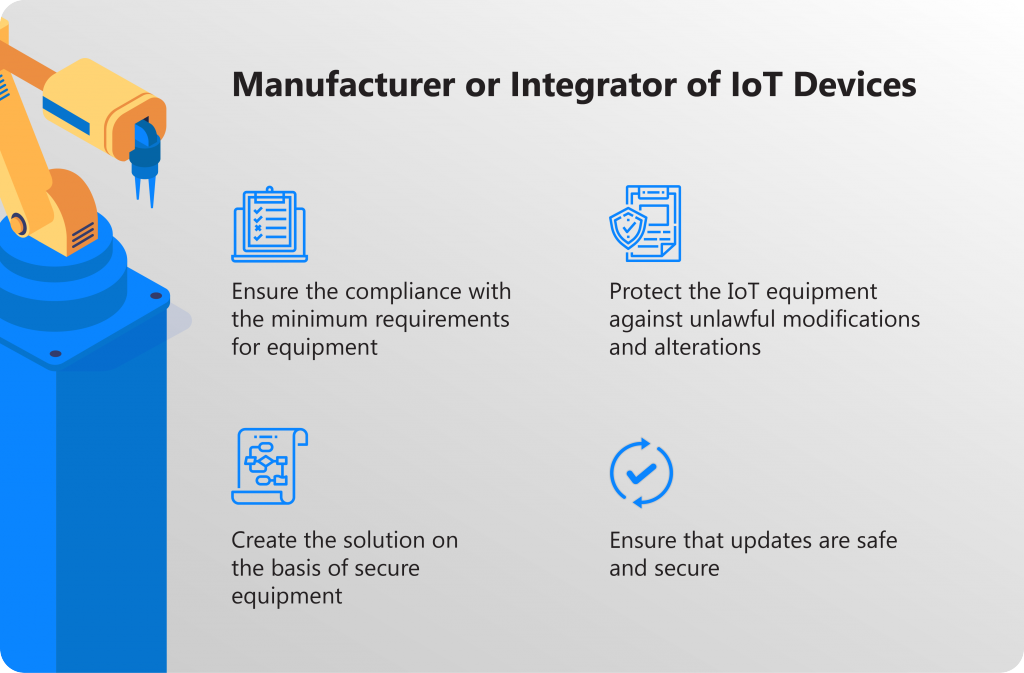
We may roughly single out the following main characters in the game called “Your IoT Project” — manufacturers/integrators of IoT devices, IoT solution/software developers, IoT solution deployment specialists and IoT solution operators (users). Of course, this list may be expanded but we wouldn’t be able to cover each and every aspect so we tried to focus on the most crucial ones. What can you do to secure Your IoT devices? Let the game begin!
Compliance with the minimum requirements for equipment
It is best if equipment contains a minimum amount of components necessary for its functioning, and nothing more. For example, you should add USB ports only if they are needed for the device to operate. Additional components open up new spots and pathways for attacks on the device and it’s obvious that we should minimize such chances.
Protection of equipment against unlawful modifications
You’d better develop procedures to identify opportunities for unlawful physical alterations, such as a loose device cover or removal of a device component. These signals pointing out to illegal penetration into the system can be sent in a data stream to the cloud, thus warning operators of these events.
Development of the solution based on secure equipment
If your budget allows, you can introduce additional security features, such as secure encrypted storage, or boot functions based on a Trusted Platform Module (TPM). These features enhance security on IoT devices and help protect the entire IoT infrastructure.
Secure updates
It is inevitable but firmware will be updated throughout the operational life of the device. The development of secure update methods and the cryptographic reliability of firmware releases will ensure the safety of devices during and after the update.
Safe software development method
When developing protected software, you need to carefully consider how to secure IoT devices at all stages — from creating the project to its implementation, testing and deployment. The method you finally choose determines platforms, languages and tools you’ll be utilizing. The secure application development lifecycle provides a step-by-step procedure to create secure software.
Caution with open-source software
This type of software accelerates the solution development process in general. However, if you opt out for this variant, you should take into account the level of community engagement in relation to each such component. If the community is active, it guarantees adequate software support and troubleshooting. Vice versa, if you use a project based on open-source software characterized by low activity and little notice, you will most likely experience lack of support, with problems left unidentified.
Caution with integration
Many vulnerabilities in the software protection system can be found at the border crossing between APIs and libraries. The functionality that is of no importance for the current deployment may still be available at the API level. To ensure the security of the entire system, be sure to check that all interfaces of integrated components are free from vulnerabilities and weak spots.
Secure equipment deployment
The situation may be that you’ll need to deploy your IoT devices in insecure locations, such as public spaces or locations with no monitoring. In this case, you should enable the utmost protection of deployed equipment from illegal modifications. If your equipment has USB or other ports, make sure they are securely covered, since they can be used as entry points for cyberattacks as well as physical alterations.
Secure authentication keys
In the process of deployment, each device requires device identifiers and associated authentication keys that are usually created by the cloud service. These keys should be stored in a physically secure location even after the deployment is over. A malicious device can use any compromised key to disguise itself as a device currently in operation.
System updates
Your OS and all device drivers must be updated to the latest version. For example, Microsoft automatically updates Windows 10 (Internet of Things or other SKUs) if the corresponding option is on. This may be the best way to secure IoT devices. Consistent upgrading of other operating systems, such as Linux, also helps protect them from malicious attacks.
Protection against malicious activity
If possible, install the latest anti-virus and anti-malware programs into the operating system of each device. This will help eliminate most of the external threats. Most modern OSs provide users with the opportunity to take timely and adequate measures and potential risks long before it even arises.
Frequent audit
To respond to security issues, you should first and foremost carry out an audit of the IoT infrastructure for security incidents. Most operating systems have built-in event logging. They should be reviewed on a frequent basis to ensure there are no security breaches. Audit data can be transmitted as a separate telemetry data stream to the cloud service for further analysis.
Physical protection of the IoT
The easiest security attacks on the IoT infrastructure occur through physical access to devices. It is of paramount importance to protect USB ports and other physically accessible components from malicious attacks. One of the key factors in detecting breaches is maintaining physical access logs, e. g. when using USB ports.
Protection of cloud credentials
Cloud authentication credentials used to configure and operate an IoT project are probably the easiest way to access an IoT system. To ensure the functioning of IoT device security solutions, you should change your password on a recurrent basis and avoid using credentials on public computers.
On a final note
Functional capabilities of all those different IoT devices vary drastically. Some devices may be represented by computers with standard desktop operating systems, while on some devices a very simplified operating system can be installed. The above safety recommendations may apply to these devices all at once or to some of them only, depending on the degree of complexity. We would strongly recommend to apply additional deployment and security recommendations provided by the device manufacturer (if any).
Some legacy and limited devices may not be designed for IoT deployment. They may not be able to encrypt data, connect to the Internet, or provide advanced audit tools. To ensure the security required when connecting such devices to the Internet, field gateways should be used when compiling data from legacy devices. The field gateway provides secure authentication, negotiation of encrypted sessions, receiving commands from the cloud, and other security features.
If you have something to add to our insights or have questions regarding the security of your IoT project, feel free to contact our support team or visit our website.